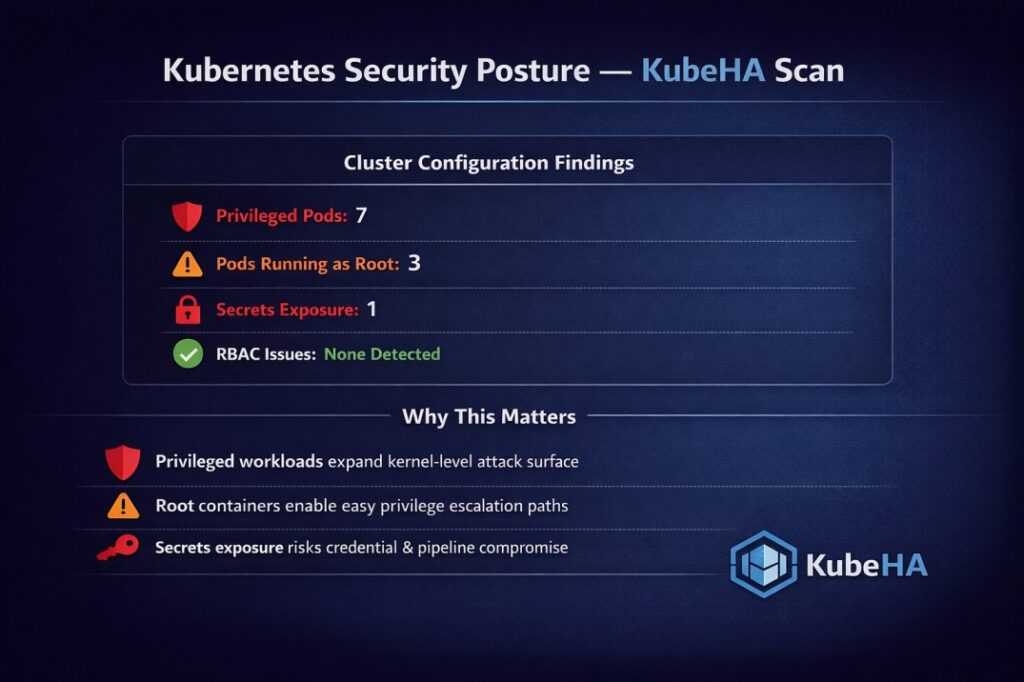
A recent KubeHA security posture scan surfaced the following runtime and configuration risks:
- Privileged Pods: 7
- Pods running as root: 3
- Secrets exposure: 1
- RBAC misconfigurations: None detected

- Privileged pods bypass key kernel isolation boundaries and significantly expand the failure and attack surface
- Containers running as UID 0 remain one of the most common causes of escalation paths in Kubernetes breaches
- Even a single exposed secret can compromise workloads, CI/CD pipelines, or control-plane access
- Clean RBAC indicates strong identity scoping – but needs continuous verification as clusters evolve

KubeHA continuously correlates:
- Security context & pod spec configs
- Runtime behavior and cluster events
- RBAC state, secrets usage, and config drift
…to highlight real risk, not just noisy violations.
This enables SRE teams to:


Kubernetes security is not a point-in-time scan.
It’s a continuous reliability problem.
Follow KubeHA (https://linkedin.com/showcase/kubeha-ara/)
Experience KubeHA today: www.KubeHA.com
KubeHA’s introduction: https://www.youtube.com/watch?v=PyzTQPLGaD0
#DevOps #sre #monitoring #observability #remediation #Automation #kubeha #IncidentResponse #AlertRecovery #prometheus #opentelemetry #grafana, #loki #tempo #trivy #slack #Efficiency #ITOps #SaaS #ContinuousImprovement #Kubernetes #TechInnovation #StreamlineOperations #ReducedDowntime #Reliability #ScriptingFreedom #MultiPlatform #SystemAvailability #srexperts23 #sredevops #DevOpsAutomation #EfficientOps #OptimizePerformance #Logs #Metrics #Traces #ZeroCode
